Network security is the process by which various components (mobile devices, computers, services, and so on) of the Network, including its data, are prevented from getting affected by malicious attacks. It is to be ensured that the services provided by the Network are not involved in its malfunctioning.
This is an overall picture of network security projects using Python.
The language is simple is preferred by many researchers to implement their network security ideas in different applications. Currently, python network security projects are becoming the trend these days owing to the user-friendly nature of the programming language. Let us first start with the network security defense systems existing today!!!!
NETWORK SECURITY THREATS AND DEFENCE SYSTEMS
The following is a brief note on different aspects of a network security system.
- Common network security threats (network, transport, physical and data link layer attacks)
- Cryptographic primitives (symmetric key and public key generation, digital signature and authentication)
- Countermeasures have to be developed for typical network attacks like jamming, location and neighbor ship spoofing and time synchronization attacks
- Securing UWAN protocols (Attack resilient Mac and routing, securing the acoustic channels)
- Security frameworks (cryptographic and security UWAN frameworks defined by software)
Primarily based on the origin and extent of the impact of an attack, it is classified as simple or complex. And based on such a classification, proper mechanisms of defense have to be constructed. We have guided a lot of Python network security projects, and we are very much knowledgeable in all the above points. Are attacks different for different networks?
NETWORKS WISE SECURITY ATTACKS
The network attacks vary with the primary nature and objective of a network. Quite importantly, it is in the hands of a software designer or a developer to take into account the various forms of attacks that the Network in question is prone to. The following are the common attacks in some of the important networks
- Mobile ad hoc networks
- Disrupting Mac
- Traffic analysis
- Sinkhole, black hole and grey hole
- Corrupting data and compromised nodes (selfish)
- Flooding SYN
- Software defined networking
- Hijacking the location of host
- Control plane and Byzantine saturation
- Overloading attacks (flow table)
- Insertion of malicious code (flow rule)
- Wireless sensor networks
- Flooding
- Selective forwarding
- Data collection
- Replicating nodes to lead malfunctioning
- Incorrect nodes and their outrage
- Vehicular ad hoc networks
- Replicating certificate and keys
- Tracking, faking of positions and GPS spoofing
- Suppressing and altering messages
- Tampering messages and broadcast
- 5G and LTE network
- Parallel session attack (FIFO)
- Stealing and reusing password
- Skimming
- Free riding
- Forgery attacks
- Mobile botnets
On many occasions, network security breaches, we have recorded many kinds of attacks. Then our engineers and developers join hands to rectify the network problems and bring them back to normal functioning instantly. So we have the requisite expertise and the essential forward and backward linkages throughout your research career. What are the latest network security research topics?
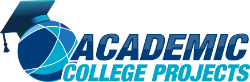
LATEST PYTHON NETWORK SECURITY PROJECTS TOPICS
The following are some of the most important and recent network security project topics
- In-vehicle network authentication of proof
- Analysis of file transfer (spatial and temporal)
- 5G anti-spoofing database (design)
- Controlling and designing secure NOC (and SOC)
- Automatic detection of attacks (in MANET)
- Hybrid variant analysis of network pattern (VANET)
- Deploying artificial intelligence systems in NFV and SDN
Conventionally researchers develop ideal systems network security, which is at times difficult to implement. As we have been in the field of guiding Python network security projects, we have witnessed a drastic shift towards adopting Python over the past two decades. Before understanding the usefulness of Python, let us see some more about the techniques and schemes available for the detection and mitigation of attacks.
ATTACK DETECTION/MITIGATION SCHEMES
Network attack detection and prevention methods are based on advanced technologies that bring in changes to both hardware and software components. The following are some of the important network attack detection and mitigation tools
- Machine learning (KNN, SVM) deep learning (CNN, DNN, LITENET) and decentralized methods (blockchain) for detecting network attacks
- Authenticating hardware (PUF), Multi factor authentication (biometrics) and channel fingerprints(CSI)
- Node isolation techniques like blocking IP, filtering packets using egress filter and deploying firewall to mitigate network attacks
Latest technologies have made highly secure network systems into reality. The methods used in the prevention and mitigation of network attacks in such systems based on various aspects as enabled by different technologies are listed below.
- Location-based techniques (privacy protection, k-means algorithm, triangle based security algorithm, confused arc SLP and source location privacy)
- Routing based security measures (stochastic routing and cuckoo search algorithm, AES and source routing)
- Trust-based mechanism (trackback, blowfish, meta-heuristic and SHA)
- Blockchain-based security systems (decentralized techniques using blockchain schemes, updating firmwares, public fee system and dist block net)
Bulks of investigation have been going on to find the use cases of many advanced technologies into network security systems. We are making coordinated efforts with researchers from top universities of the world to conclude on quality solutions to specific network attacks in crafting network security thesis. So we are very much familiar with the essentials for Python network security projects like the famous data sets as mentioned below.
FAMOUS DATASETS FOR NETWORK ATTACKS
- KDD 99 and KDD CUP’99
- NSL KDD
- N BaIoT
- ADFA – LD
- IEEE 118
- DS2OS
Own datasets synthesized for customized purposes are also encouraged. Reach out to our technical team to initiate your proceedings for the synthesis of particular data sets. Now latest talk on Python for network security applications.
PYTHON FOR NETWORK SECURITY – PURPOSE AND BENEFITS
- Python is an easy to use multipurpose programming language used mostly in the server side of network security projects.
- It is taken up by developers on a large scale primarily because it does not need third party applications and tools for programming support.
It is important for present-day Network researchers to be familiar with Python irrespective of their topic. What are the major advantages of Python?
ADVANTAGES OF USING PYTHON
Python is a great tool to be used in network security projects for its following advantages.
- Socket programming imports the socket and invoke them
- Data extraction from social media in real time by ensuring cyber security
- Extracting geo location using ‘pygeoip’ module which uses Google API to identify real-time position using IP address
- Packet sniffing using wireshark and other python codes which are implemented with the help of NIC (for local Network traffic sniffing)
- Scanning network ports using python nmap tool without involving third party applications
We support in all aspects from basic to advance in understanding and implementing python programs. So you can confidently rely on him for your entire research.
What Are The Attacks Detected Using Python?
Python can be used to detect common and serious network attacks like code exploitation, social engineering, port scanning, botnets, exposure of critical information, scripting across sides, and SQL injection.
As now well known, Python is the best, both as a programming language and as a simulation tool, for researches doing projects in network security. We are here to provide you full support for all topics on Python-based network security systems. What are the recent Python-based research ideas in network security?
Network Security Research Ideas using Python
The following are some of the major trending research topics in network security that can be implemented using Python
- Analyzing vulnerability, network traffic, scanning port and wireless networks for security
- Cloud Security and protection from phishing
- Mitigation of vulnerabilities in web applications
- Remediation of antivirus evasion
- Authenticating multiple factors
- Fingerprinting web servers
- Simulation of attacks and mail server access
- Testing websites and generation of attacks
- Systems for preventing and detecting intrusions
You can expect research support starting from the choice of topic till the paper is published on all the above research ideas. Now let us have some ideas on python network security projects that have good future scope
Important Network Security Topics Using Python
Does using Python ensure the future scope of research in network security projects? The following are the major network security topics using Python that have the potential for future research.
- 5G physical layer network security
- Integrated systems for detecting, preventing and response to intrusions
- Analysis of dependability and security
- Emerging technologies for ensuring security and privacy like cognitive radio networks, MIMO systems, UAS, mmwave, spectrum sharing, smart systems and so on
- Implementing and evaluating network security systems
- Management and analysis of risks
- Management of key, authentication and certification, public key infrastructure
- Security in different network types like ad hoc, sensor, body area, delay tolerant, mesh, Wi-Fi, ad hoc, social networks and so on
Order to test the implementation of these emerging technologies into network security systems requires the use of simulation tools. How would you choose the best simulator for your network security project? The simulation tools can be compared on the basis of the following grounds
- Range of simulation
- Node specification
- Node links
- Traffic among different nodes
- Protocols used for analyzing and handling traffic
- Graphical techniques used in visualizing the simulation environment and its working
Here it is quite important to understand that the python network simulator is a more advanced and suitable tool for Python Network security projects these days. Consider the following points on the python simulator.
- It contains many different simulators based on the python language
- Easy to use and learn
- Length of the code is less compared to C ++ and java
We have a dedicated team of technical and research experts to guide you in handling these tools. We also render proper code implementation guidance and help you in improving the project at every stage of its development. What are the network simulation tools based on Python?
PYTHON NETWORK SIMULATION TOOLS
The network simulation tools are very important to determine the performance of your project. In this regard, the tool that you choose must be in line with the language that you choose for writing algorithms and protocols. Refer to the following list of simulation tools that are based on Python.
- NS 3 using python and C++ – It is an open source environment for simulation can be made using the networks both dependent and independent on IP. LTE, Wi-Fi and wimax networks (IP simulation)
- OMNET ++ – IP model architecture based on different components (or modules). It is an event network simulator using python with SUMO integration on VANET environment (traffic model)
- Mininet – It is an open source software and network emulator used in research, development, prototyping, learning and testing. It is used in various link routers switches and end hosts (single Linux kernel)
- Graphical Network simulator 3 or GNS3 – It is used in simulating the performance of HTTP server in times of DDoS attacks (Modeling the DDoS attacks is complex)
- TOSSIM – it helps in network interaction mechanisms in TinyOS sensor networks’ packets traffic monitoring (on statistics and dynamics). It is a discrete event simulation based on python and C++
- Fast Network simulation setup or FNSS – It is an efficient toolchain used for network scenario setting. The tool is used in the following aspects.
- Link configuration (weights, size of the buffer, delay, capability and so on)
- Generation of traffic matrices and event scheduling
- Deployment of protocols and applications (on nodes)
- Generation of topology and datasets based on synthetic models
- Network deployment and configuration of workload (for different emulators and simulators)
- It has core library and adapters for experiment scenarios creation
The adapters in FNSS are also used in exporting the simulation environment generated to other simulators like Mininet, NS 2, Autonetkit, OMNET++, NS 3, jFed, and so on. You are also allowed to export scenarios that are generated using the core libraries of the above-mentioned simulators other simulation and emulation tools using Python, Java, and C + + core libraries
$ pip fnss is the command which is used to install FNSS (using pip)
We hope the ideas that you gained from this article will give you to an elevated interest in doing network security projects using Python. If yes, then reach out to our page on python network security projects to set up an illustrious career for you. Our experts are happy to help you in bringing out your ideas into reality.